Allowing Remote Access to the GUI¶
Several ways exist to remotely administer a firewall running pfSense® software that come with varying levels of recommendation. They all work, but their use may vary for any number of reasons (Client restrictions, corporate policies, etc.)
Use a VPN¶
The safest way to accomplish the task is to set up a VPN that will allow access to the firewall and the network it protects. There are several VPN options available in pfSense software, such as
Once a VPN is in place, reach the GUI safely using a local address on the firewall, such as the LAN IP address. The exact details vary depending on the VPN configuration.
Restricted Firewall Access¶
If the GUI port must be accessible to the Internet, restrict it by IP address or range as much as possible. Ideally, if there is a static IP address at the location to manage from, allow traffic from that IP address or subnet and nowhere else. Aliases also help, and they can include fully qualified domain names as well. If the remote management clients have a dynamic DNS address, add it to a management alias.
Use HTTPS¶
The best practice is to always use HTTPS to encrypt access to the GUI port. Modern browsers may complain about the certificate, but an exception can usually be stored so it will only complain the first time.
To disable (or re-enable) HTTPS for the GUI, navigate to System > Advanced, under the Admin Access tab, using the Protocol option in the webConfigurator section. See Admin Access for details.
Move the GUI to an Alternate Port¶
Moving the GUI to a non-standard, random port is also beneficial. This does not improve the actual security of the GUI itself, but can potentially reduce the number of brute force attempts. The GUI can still be found by scanners unless the port is properly filtered.
The port for the GUI can be changed under System > Advanced, Admin
Access tab, using the TCP Port option in the webConfigurator section.
Avoid common ports like 443, 31337, 8080, 8888, etc.
Strict Management¶
To enhance the security of a network, in many environments access to the firewall GUI is limited by firewall rules. Restricting access to the management interface is the best practice, for reasons as to why, see the blog post Securely Managing Web-administered Devices.
The default configuration of pfSense software allows management access from any machine on the LAN and denies it to anything outside the local network. There is also an anti-lockout rule enabled by default that prevents firewall rules from being configured in a way that will lock the user out of the web interface.
To restrict management access first ensure the LAN rules allow access to the port used for the GUI. This depicts the default LAN rule, which allows access to the web interface.
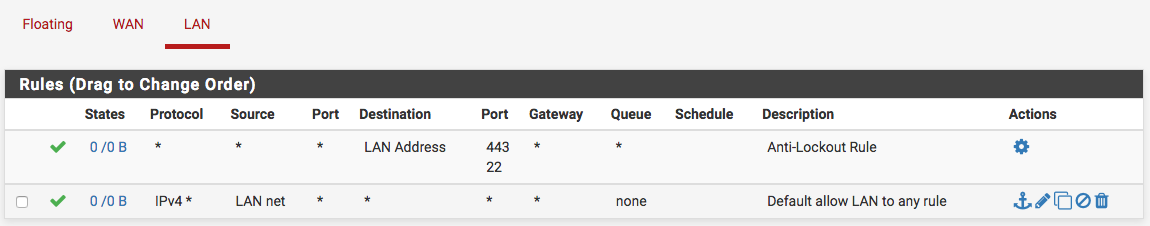
If a restrictive ruleset is in place on the LAN, make sure it permits access to the web interface before continuing.
Now disable the anti-lockout rule. Navigate to System > Advanced, Admin Access tab and check Disable webConfigurator anti-lockout rule. Click Save and the rule will be removed.
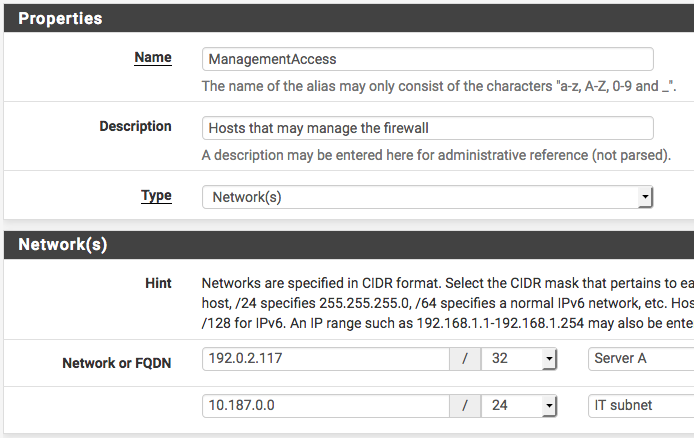
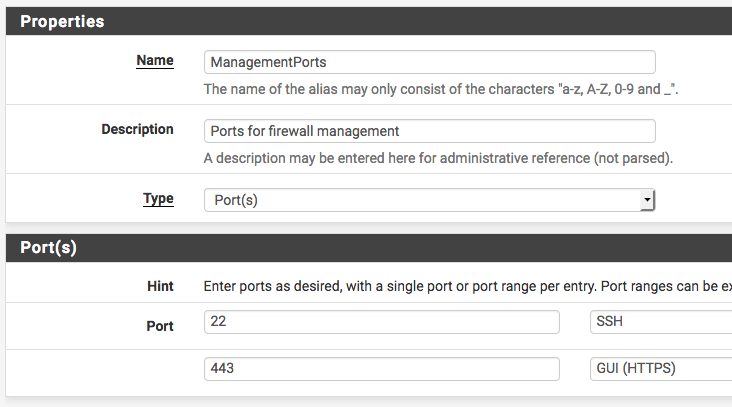
Using a network alias for management access is another useful best practice. If both web and SSH administration are used, add an alias for those ports. The following are examples:
1. Example alias for networks allowed to access management interface
2. Example alias for ports allowed to access management interface
Now add a firewall rule allowing the sources defined in the management alias to
the destination of the firewall, with the port used or alias created for those
using multiple ports. Make sure this rule is first in the list. Then add a
rule based on that rule (click  next to the rule), changing action to
block or reject (reject is preferred on internal networks), source to any,
and destination the same. When finished the ruleset should look like the
following.
next to the rule), changing action to
block or reject (reject is preferred on internal networks), source to any,
and destination the same. When finished the ruleset should look like the
following.
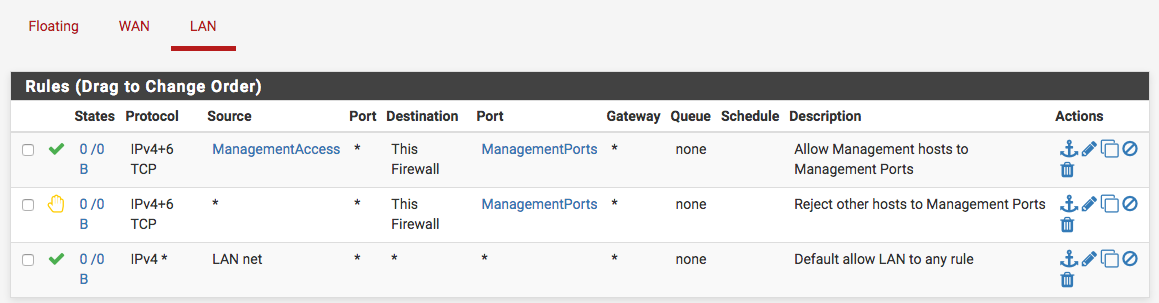
Click Apply Changes and the management interface is now restricted to only the defined hosts.
I Don’t Care About Security, How Do I Open Access To The GUI?¶
To open the firewall GUI, create a firewall rule to allow remote firewall administration.
Note
Do not create a port forward or other NAT configuration.
Firewall > Rules, WAN Tab
- Action:
pass
- Interface:
WAN
- Protocol:
TCP
- Source:
The IP address or subnet of the client, an alias containing management hosts/networks, or (as a last resort only) Any
- Destination:
WAN Address
- Destination port range:
HTTPS (Or the custom port)
- Description:
Allow remote management from anywhere (Dangerous!)