Configuring IPv6 Through A Tunnel Broker Service¶
A location that does not have access to native IPv6 connectivity may obtain it using a tunnel broker service such as Hurricane Electric. Similarly, a core site with IPv6 can deliver IPv6 connectivity to a remote site by using a VPN or GIF tunnel.
This section provides the process for connecting pfSense® software with
Hurricane Electric (Often abbreviated to HE.net or HE) for IPv6 transit. Using
HE.net is simple and easy. It allows for multi-tunnel setup, each with a
transport /64 and a routed /64. Also included is a routed /48 to be
used with one the tunnels. It is a great way to get a lot of routed IPv6 space
to experiment with and learn, all for free.
Sign Up for Service¶
ICMP echo requests must be allowed to the WAN from the tunnel broker server, or it cannot function. A rule to pass ICMP echo requests from a source of any is an acceptable temporary measure. Once the tunnel endpoint for HE.net has been chosen, the rule can be made more specific.
To get started on HE.net, sign up at www.tunnelbroker.net. HE.net will
allocate /64 networks after registering and selecting a regional IPv6 tunnel
server.
A summary of the tunnel configuration can be viewed on HE.net’s website as seen in Figure HE.net Tunnel Config Summary. It contains important information such as:
- Tunnel ID:
A number to uniquely identify this tunnel.
- Server IPv4 Address:
IP address of the HE.net tunnel server
- Client IPv4 Address:
The external IP address of the firewall
- Server IPv6 Addresses:
The IPv6 address used inside the tunnel for the remote endpoint.
- Client IPv6 Addresses:
The IPv6 address used inside the tunnel for this firewall.
- Routed IPv6 Prefixes:
The IPv6 prefixes routed to the firewall over this tunnel. By default, there is at least a
/64prefix listed, but HE.net can also allocate a/48upon request.
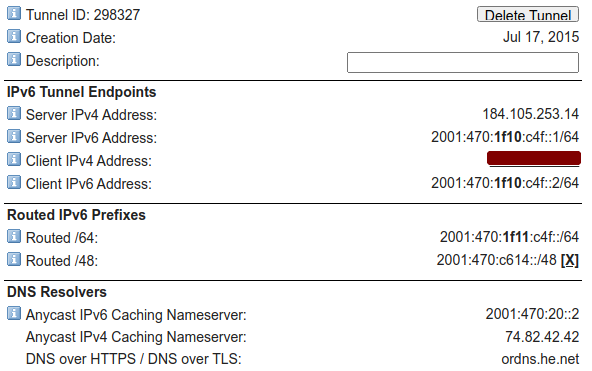
HE.net Tunnel Config Summary¶
The Advanced tab on the tunnel broker site has two additional notable options:
- MTU:
The MTU for packets sent by HE.net over the tunnel.
If the WAN used for terminating the GIF tunnel is PPPoE or another WAN type with a low MTU, move the slider down as needed. For example, a common MTU for PPPoE lines with a tunnel broker is
1452.- Update Key:
A key for updating the tunnel address using dynamic DNS mechanisms.
If the WAN has a dynamic IP address (e.g. DHCP, PPPoE), note this key for later use.
Once the initial setup for the tunnel service is complete, configure the firewall to use the tunnel.
Allow IPv6 Traffic¶
New installations of pfSense software allow IPv6 traffic by default. Configurations upgraded from older versions may still be set to block IPv6.
To enable IPv6 traffic, perform the following:
Navigate to System > Advanced on the Networking tab
Check Allow IPv6 if not already checked
Click Save
Allow ICMP¶
The firewall must allow ICMP echo requests on the WAN address that is terminating the tunnel. This allows HE.net to ensure that the firewall is online and reachable. If the firewall blocks ICMP the tunnel broker may refuse to set up the tunnel to the IPv4 address.
Edit the ICMP rule created earlier, or create a new rule to allow ICMP echo requests from a source IP address of the Server IPv4 Address in the tunnel configuration as shown in Figure Example ICMP Rule.
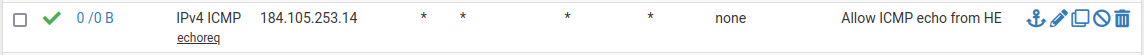
Example ICMP Rule¶
Create and Assign the GIF Interface¶
Next, create the interface for the GIF tunnel. Complete the fields with the corresponding information from the tunnel broker configuration summary.
Navigate to Interfaces > Assignments on the GIF tab
Click
 Add to add a new entry
Add to add a new entryConfigure the settings as follows:
- Parent Interface:
The WAN where the tunnel terminates. This would be the WAN which has the Client IPv4 Address on the tunnel broker.
- GIF Remote Address:
The Server IPv4 Address on the summary.
- GIF Tunnel Local Address:
The Client IPv6 Address on the summary.
- GIF Tunnel Remote Address:
The Server IPv6 Address on the summary, along the with prefix length (typically
/64).- Description:
Text describing the tunnel, such as
HE Tunnel Broker
Leave remaining options blank or unchecked
Click Save
See Figure Example GIF Tunnel.
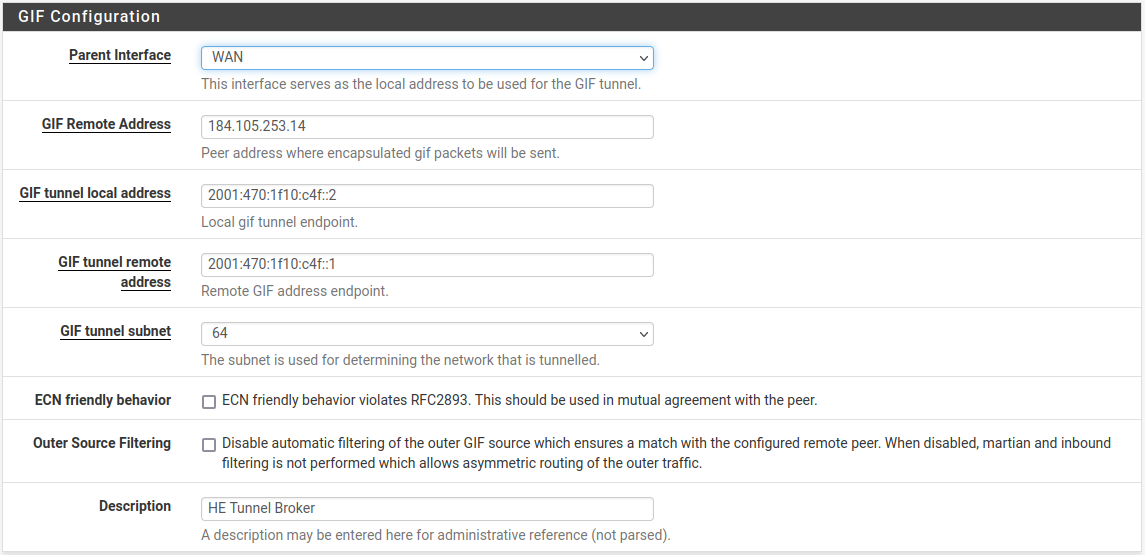
Example GIF Tunnel¶
Note
If the WAN containing this tunnel uses a dynamic IP address, see Updating the Tunnel Endpoint for information on how to keep the tunnel endpoint IP address updated with HE.net.
Now assign the GIF tunnel as an interface:
Navigate to Interfaces > Assignments, Interface Assignments tab
Select the newly created GIF under Available Network Ports
Click
 Add to add it as a new interface
Add to add it as a new interface
Configure the New OPT Interface¶
The new interface is accessible at Interfaces > OPTx, where x is a
sequential number assigned to the interface.
Navigate to the new interface configuration page. (Interfaces > OPTx)
Check Enable Interface
Enter a name for the interface in the Description field, e.g.
WANv6Click Save
Click Apply Changes
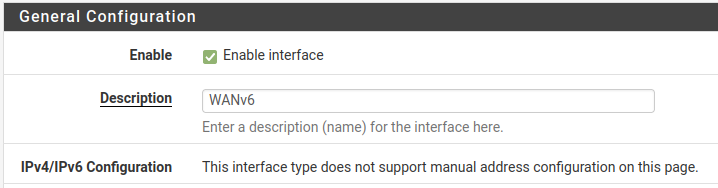
Example Tunnel Interface¶
Warning
After applying the interface changes the firewall may need to be restarted before the interface configuration will be fully operational. Check Status > Interfaces and if the IPv6 Address field is missing or empty for the assigned GIF interface, reboot the firewall.
Set up the IPv6 Gateway¶
The firewall automatically creates a dynamic IPv6 gateway for the assigned GIF interface, but it is not yet marked as default.
Navigate to System > Routing
Set Default Gateway IPv6 to the dynamic IPv6 gateway with the same name as the IPv6 WAN created above (e.g.
WANV6_TUNNELV6)Click Save
Click Apply Changes
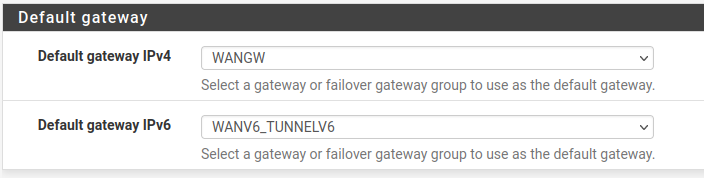
Example Tunnel Gateway¶
Navigate to Status > Gateways to view the gateway status. The gateway will show as “Online” if the tunnel is operational, as seen in Figure Example Tunnel Gateway Status.
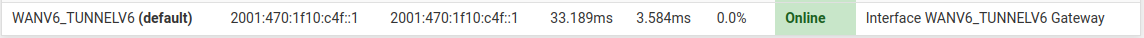
Example Tunnel Gateway Status¶
Setup IPv6 DNS¶
The firewall DNS configuration likely already properly handles DNS queries for
AAAA records already. If the firewall is configured to use
the DNS Resolver in resolver mode, which is the default, then
nothing needs to be done.
If the firewall is configured to use the DNS Resolver in forwarding mode, or it uses the DNS Forwarder, then the best practice is to add the tunnel broker DNS Servers under System > General Setup.
Enter at least one IPv6 DNS server or use a public DNS service such as Google
public IPv6 DNS servers (2001:4860:4860::8888, 2001:4860:4860::8844),
Quad9, or CloudFlare.
At this point the firewall itself should have full working IPv6 connectivity.
Setup LAN for IPv6¶
For clients on LAN to access the internet using IPv6, the LAN must also be configured for IPv6.
The most common method is to set LAN as dual stack IPv4 and IPv6.
Navigate to Interfaces > LAN
Change the configuration as follows:
- IPv6 Configuration Type:
Static IPv6
- Static IPv6 Configuration:
Enter an IPv6 address from the Routed /64 in the tunnel broker configuration with a prefix length of
64.For example, use
2001:db8:1111:2222::1for the LAN IPv6 address if the Routed /64 is2001:db8:1111:2222::/64.
Click Save
Click Apply Changes
Alternately, use a /64 from within the Routed /48 prefix.
Setup DHCPv6 and/or Router Advertisements¶
Router Advertisements and/or DHCPv6 can assign IPv6 addresses to clients automatically. This is covered in detail in IPv6 Router Advertisements.
A brief overview is as follows:
Navigate to Services > DHCPv6 Server
Change to the local interface where IPv6 clients are located
Check Enable
Enter a range of IPv6 IP addresses inside the new LAN IPv6 prefix
Click Save
Navigate to Services > **Router Advertisement
Change to the local interface where IPv6 clients are located
Set the Mode to Managed (DHCPv6 only) or Assisted (DHCPv6+SLAAC)
Click Save
Modes are described in greater detail at Router Advertisements (Or: “Where is the DHCPv6 gateway option?”).
To assign IPv6 addresses to LAN clients manually, use the firewall LAN IPv6 address as the gateway with a proper matching prefix length, and pick addresses from within the LAN prefix.
Add Firewall Rules¶
Now add firewall rules which allow IPv6 traffic from hosts on LAN.
Note
The default LAN ruleset on current installations already contains a rule to pass IPv6, but the best practice is to check and confirm it is present and configured appropriately.
Navigate to Firewall > Rules, LAN tab.
Check the list for an existing IPv6 rule
If a rule to pass appropriate IPv6 traffic already exists, then no additional action is necessary.
Click
 Add to add a new rule to the bottom of the list
Add to add a new rule to the bottom of the listConfigure the rule as follows:
- Address Family:
IPv6
- Source:
LAN Net
- Destination:
Any
Click Save
Click Apply Changes
If a local interface contains servers which need to handle public IPv6 requests, add firewall rules on the tab for the IPv6 WAN (the assigned GIF interface) to allow IPv6 traffic to reach the servers on required ports.
Reboot¶
The best practice is to restart the firewall and then the clients before testing connectivity.
Reboot the firewall first using Diagnostics > Reboot. Monitor the boot process for errors and check the interface and gateway status once it is back online. This not only ensures that the firewall is configured properly but will also be configured correctly on subsequent reboots.
Next, reboot a client to test. Some clients may automatically obtain an IPv6 address while they are up and running, some may need their networking services restarted, and others will only check at boot time. Thus, the best practice is to reboot the client to ensure it obtains IPv6 configuration parameters from the firewall.
Note
If a client does not obtain an IPv6 address, check its network settings to see if IPv6 connectivity is enabled and active. Additionally, some clients do not implement certain types of IPv6 configuration. For example, Android clients are not compatible with DHCPv6, but they can use SLAAC.
Try It!¶
Finally, check for IPv6 connectivity using a site such as test-ipv6.com. An example of the output results of a successful configuration from a client on LAN is in Figure IPv6 Test Results.
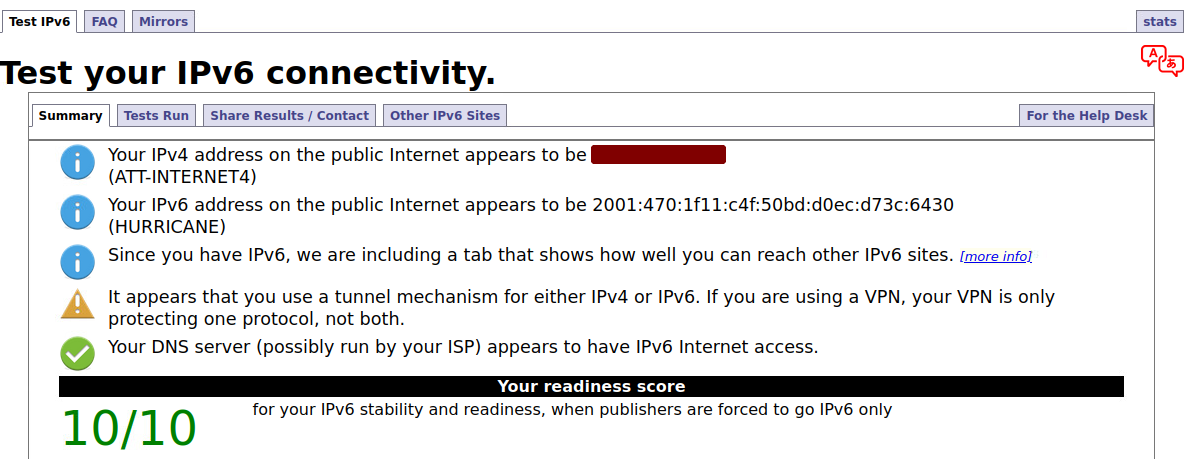
IPv6 Test Results¶
Updating the Tunnel Endpoint¶
The firewall can still use HE.net as a tunnel broker on dynamic WAN types such as DHCP or PPPoE. pfSense software includes a Dynamic DNS type which updates the tunnel endpoint IP address whenever the WAN interface IP changes.
If necessary, configure Dynamic DNS as follows:
Navigate to Services > Dynamic DNS
Click
 Add to add a new entry
Add to add a new entryConfigure the entry as follows:
- Service Type:
HE.net Tunnelbroker
- Interface to Monitor:
WAN
- Hostname:
Enter the Tunnel ID from the tunnel broker configuration.
- Username:
The Username for the tunnel broker site.
- Password:
Enter either the Password or Update Key for the tunnel broker site.
- Description:
Text describing the entry, e.g.
HE Tunnel
Click Save and Force Update
If and when the WAN IP address changes, the firewall will automatically update the tunnel broker configuration.