Adding OpenVPN Remote Access Users¶
The method for adding users to the VPN depends upon the OpenVPN server authentication method and backend (e.g. Local Database, RADIUS, LDAP).
See also
Local Database¶
OpenVPN authenticates local database users based on their entries in the user manager.
To create a new user with a certificate, follow these steps:
Navigate to System > User Manager
Click
 To add a user
To add a userFill in the settings as follows:
- Username:
The username for this client.
- Password/Confirm password:
The password for this client.
- Full Name:
An optional longer name for this user.
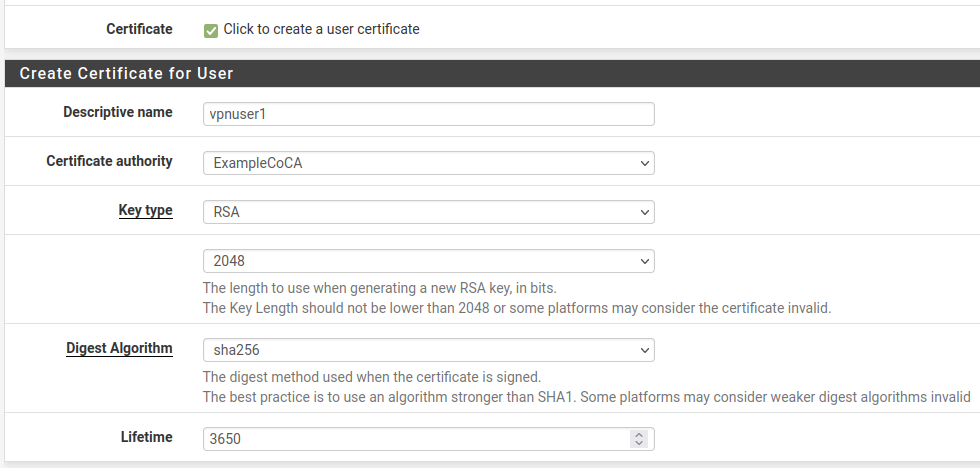
- Click to create a user certificate:
Checked
- Descriptive Name:
Same value as the Username
- Certificate Authority:
The CA used by the OpenVPN server.
- Key Type:
The type of private key to use for this certificate, either RSA or ECDSA and its accompanying Key Length (RSA) or Curve (ECDSA). The default is an acceptable choice.
- Lifetime:
The number of days for which the certificate is valid. The default of
3650(approximately 10 years) is acceptable for a user certificate.
Click Save
To view or change the user:
Navigate to System > User Manager
Click
 next to the row containing the user to see/edit
next to the row containing the user to see/edit
To export a user certificate and key:
Note
The OpenVPN Client Export Package (OpenVPN Client Export Package) can package up the certificates and other data automatically. The client export package is a much easier way to download client configurations and installation files than exporting these items manually.
Navigate to System > Certificates, Certificates tab
Locate the user certificate in the list
Click
 to download the user certificates
to download the user certificatesClick
 to download the key for the certificate
to download the key for the certificateTip
To password protect the private key, edit the certificate, enter an Export Password, and click Export Private Key on that page.
Click
 to download a PKCS#12 bundle which includes the user
certificate and key, and the CA Certificate (optional).
to download a PKCS#12 bundle which includes the user
certificate and key, and the CA Certificate (optional).Tip
To password protect the PKCS#12 bundle, edit the certificate, enter an Export Password, and click Export PKCS#12 on that page.
Most use cases which utilize a user certificate will also require the CA Certificate which signed the user certificate. Export the CA certificate from its entry on System > Certificates, CAs tab or use one of the PKCS#12 bundle options.
LDAP or RADIUS Users¶
Adding LDAP and RADIUS users fully depends on the server implementation and management tools, which are beyond the scope of this documentation. Contact the server administrator or software vendor for assistance.
Certificates for LDAP or RADIUS users cannot be created from within the firewall GUI in a way that reflects a user-certificate relationship, but they can be created independently as user certificates in the certificate manager. Create user certificates with the certificate manager as described in User Certificates