Additional protection for a wireless network¶
In addition to strong encryption from WPA2 with AES, some users like to employ an additional layer of encryption and authentication before allowing access to network resources. The two most commonly deployed solutions are Captive Portal and Virtual Private Networks. These methods can be employed whether an external access point is used on an OPT interface or an internal wireless card as the access point.
Note
In theory, The PPPoE server could also be used in this role, but implementation would be impossible on some clients and non-trivial on most others, so it is not typically a viable option when combined with wireless.
Additional wireless protection with Captive Portal¶
By enabling Captive Portal on the interface where the wireless resides, authentication can be required before users may access network resources beyond the firewall. In corporate networks, this is commonly deployed with RADIUS authentication to Microsoft Active Directory, so users can use their Active Directory credentials to authenticate while on the wireless network. Captive Portal configuration is covered in Captive Portal.
Note
If the sole requirement is per-user RADIUS authentication, a better solution for RADIUS is 802.1X rather than using Captive Portal, unless there are clients present which are not compatible with 802.1X.
Captive Portal is more likely to be used on open or limited access wireless networks, such as those in a hotel, restaurant, or similar setting where there is either no encryption enabled or a common knowledge/shared key.
Additional protection with VPN¶
Adding Captive Portal provides another layer of authentication, but does not offer any additional protection from eavesdropping of wireless traffic. Requiring a VPN connection before allowing access to the internal network and Internet adds another layer of authentication as well as an additional layer of encryption for wireless traffic. The configuration for the chosen type of VPN will be no different from a remote access configuration, but the firewall rules must be configured on the pfSense® interface to only allow VPN traffic from wireless clients.
Configuring firewall rules for IPsec¶
Figure Rules to allow only IPsec from wireless shows the minimal rules required to allow only access to IPsec on the WLAN interface IP address. Pings to the WLAN interface IP address are also allowed to assist in troubleshooting.
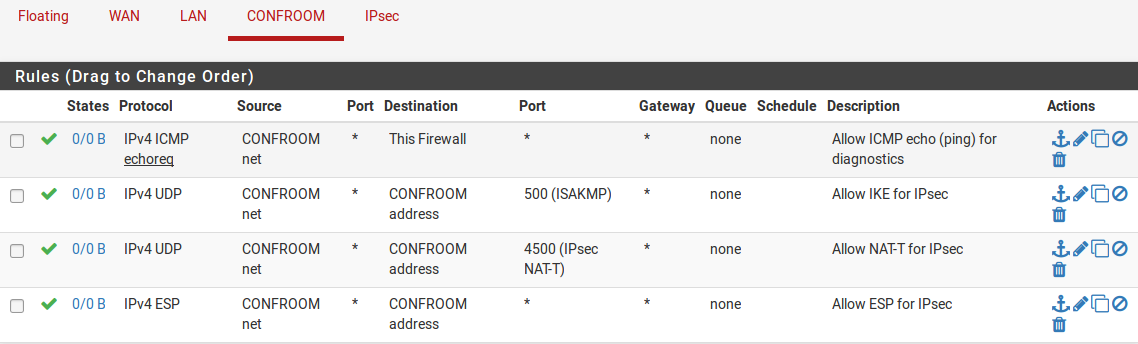
Rules to allow only IPsec from wireless¶
Configuring firewall rules for OpenVPN¶
Figure Rules to allow only OpenVPN from wireless shows the minimal rules required to allow access only to OpenVPN on the WLAN interface IP address. Pings to the WLAN interface IP address are also allowed to assist in troubleshooting. This assumes the default UDP port 1194 is in use. If another protocol or port was chosen, adjust the rule accordingly.
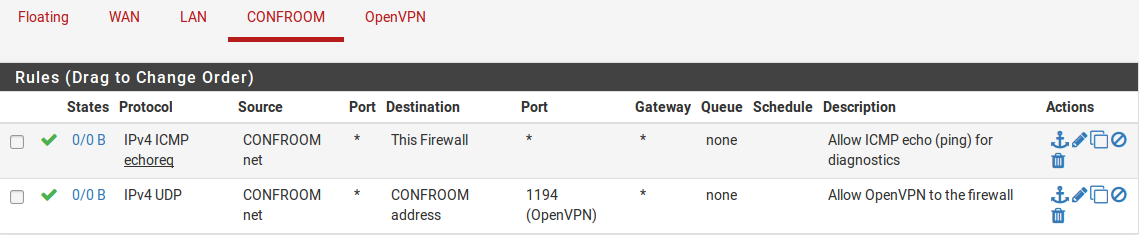
Rules to allow only OpenVPN from wireless¶