Alias Types¶
The next sections describe the behavior of each alias type in detail. Any type-specific configuration settings are also covered in these sections.
Built-In System Aliases¶
pfSense® software includes several built-in System Aliases which are accessible to users. These include stock collections of networks and IP addresses as well as automatically generated and/or maintained collections.
These are visible on the All tab under Firewall > Aliases in the System Aliases section.
Note
Some of these System Aliases have multiple variations for IPv4, IPv6, and
combined IPv4+IPv6. These are denoted by the number 4, 6 or 46
near the end of the name, respectively. In most cases it is safe to use the
IPv4+IPv6 version as the firewall will use whichever address family is
appropriate for a rule, but some users may prefer to
configure different rules for IPv4 and IPv6.
The current list includes the following entries:
- bogons:
- sshguard:
Hosts blocked by anti-brute-force login protection for SSH and the GUI.
- snort2c:
Hosts blocked by IDS/IPS software.
- virusprot:
Hosts which tripped firewall rate limit protections in advanced options (e.g. maximum source hosts for a rule).
- _nexus_vpn_port_:
Netgate Nexus VPN port (Netgate Nexus).
- vpn_networks:
Networks for IPsec, OpenVPN, and PPPoE servers.
Note
This may not be complete as it cannot detect networks made available via dynamic routing, pushed routes from OpenVPN, advanced/custom options, etc.
- negate_networks:
Networks to exclude from policy routing rules with any destination.
- tonatsubnets:
Networks for which the firewall will apply outbound NAT in Automatic and Hybrid modes.
- _loopback(4|6|46)_:
Local loopback addresses.
- _linklocal(4|6|46)_:
Link-local addresses which must not leave their own network.
- _private(4|6|46)_:
“Private” network allocations common for local private networks.
- _multicast(4|6|46)_:
Multicast networks.
- _reserved(4|6|46)_:
All current known reserved networks.
Host Aliases¶
Host type aliases contain entries consisting of individual IP addresses or fully qualified domain names (FQDNs).
When creating an alias, users may enter an IP address range such as
192.168.1.1-192.168.1.10 or a small subnet such as 192.168.1.16/28. When
saving the alias, the firewall translates that specification into a list of
individual IP addresses.
Figure Example Hosts Alias shows an example of a host type alias which contains a list of public web servers.
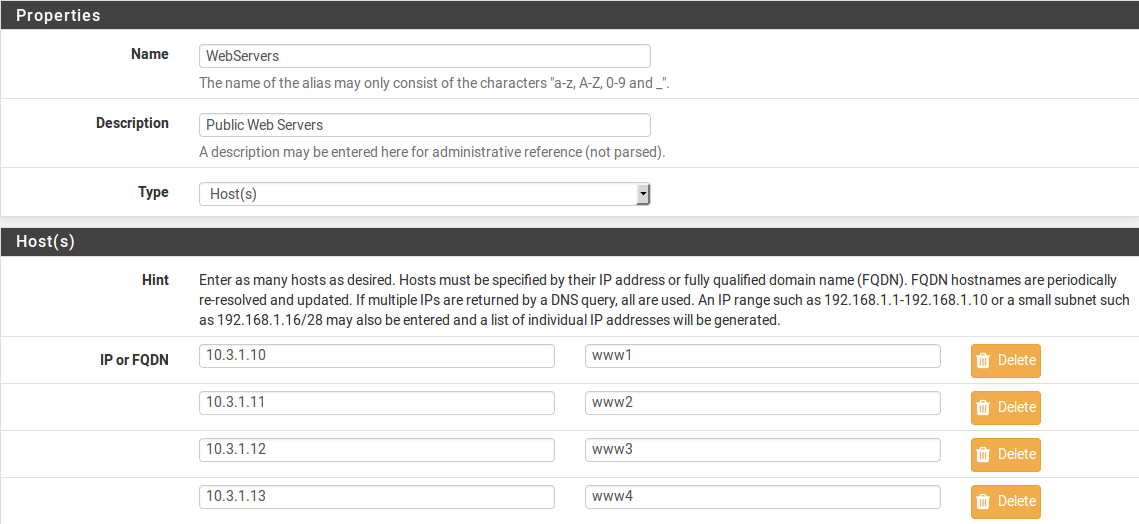
Example Hosts Alias¶
Network Aliases¶
Network type aliases contain entries consisting of CIDR format networks/prefixes or fully qualified domain names (FQDN) for single addresses.
For subnets, select the CIDR mask that pertains to each entry. /32 specifies
a single IPv4 host, /128 specifies a single IPv6 host, /24 specifies
255.255.255.0, /64 specifies a normal IPv6 network, etc.
Hostnames (FQDNs) may also be specified, using a /32 mask for IPv4 or
/128 for IPv6. This mask is not applied to addresses returned by DNS.
Figure Example Network Alias shows an example of a network alias.
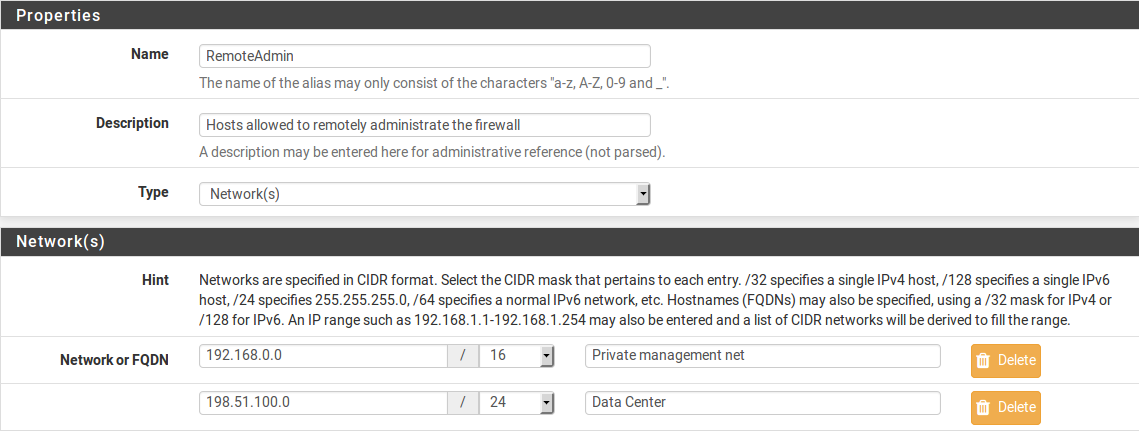
Example Network Alias¶
When an alias entry contains an IPv4 range the firewall automatically translates the range to an equivalent set of IPv4 CIDR networks which exactly contain the range. This is shown in Figure Example IP Range After.

Example IP Range Before¶
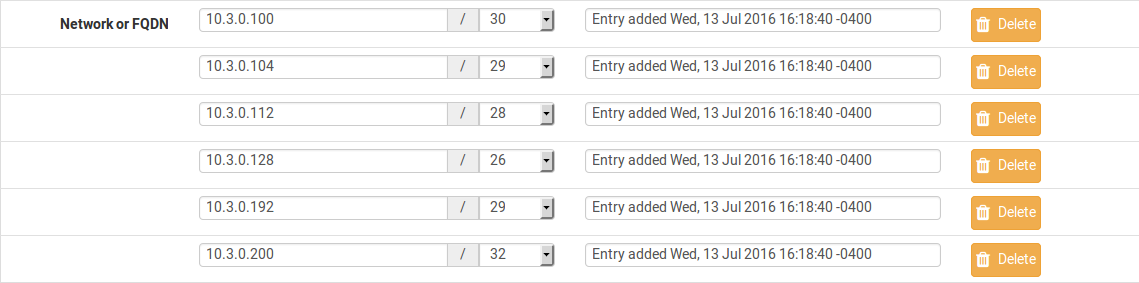
Example IP Range After¶
Port Aliases¶
Port type aliases contain entries consisting of ports numbers and port ranges.
A single port is an integer from 1-65535. A port range is two ports
separated by a colon (:), for example, 1194:1199. Port ranges match the
specified start and ending port numbers and all ports in between.
Port aliases do not have a direct relationship with any protocol. Firewall rules using a protocol of TCP, UDP, or SCTP may use port aliases to match port numbers for the protocol on the rule.
Figure Example Ports Alias shows an example of a port type alias.
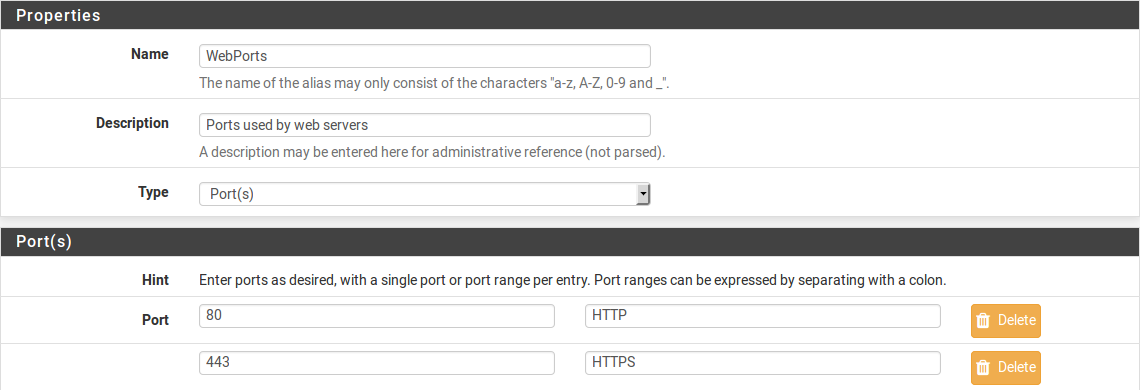
Example Ports Alias¶
URL Aliases¶
URL type aliases contain one or more URLs which return a plain text a list of entries.
When creating the alias, the firewall reads up to 3,000 entries from each URL and imports them into an alias.
The exact behavior depends on the type of URL alias:
- URL (IPs):
The URLs must contain IP addresses, CIDR masked network entries, or FQDNs. The firewall creates a Network type alias from the content.
- URL (Ports):
The URL must contain only port numbers or port ranges. The firewall creates a Port type alias from the content.
URL Table Aliases¶
URL Table type aliases contain one or more URLs which return a plain text a list of entries, plus an update interval which indicates how frequently the firewall should re-fetch the URL contents.
URL Table type aliases download the content of the URLs into a special location
on the firewall, then use that content for a persist table, also known as a
file-based alias. The full contents of these alias are not directly editable in
the GUI, but the GUI can display the Firewall Table Contents.
The drop-down list after the / in an entry of a URL Table alias controls the
number of days after which the firewall re-fetches content from the stored URLs.
The firewall checks once per day to determine if URL table aliases need updates.
URL Table aliases can be quite large, containing many thousands of entries. Some customers use them to hold lists of all IP address blocks in a given country or region, which can easily surpass 40,000 entries. The pfBlockerNG package uses this type of alias when handling country lists and other similar actions.
The exact behavior depends on the type of URL alias:
- URL Table (IPs):
The URLs must contain IP addresses, CIDR masked network entries, or FQDNs. The firewall creates a Network type alias from the content.
- URL Table (Ports):
The URL must contain only port numbers or port ranges. The firewall creates a Port type alias from the content.